Picture this scenario: You’re on a Zoom call with a client, and you notice their lips moving, but there’s a substantial delay before you hear their voice.
While you are speaking, they keep complaining about the same thing.
You are proposing a solution to a client that has several variable parts. To help explain it visually, your team has created an infographic. However, when you try to upload the image, it takes too long to load. Moving from one screen to another takes much time due to the slow loading process.
You are not satisfied with your experience. Your team has confirmed that the internet is working properly, and there are no issues on the provider’s side.
Network congestion can lead to various such issues.
Network equipment may drop packets (data packets containing information) during congestion. Packet loss can disrupt data flow, causing gaps in audio or video streams, incomplete downloads, or interruptions in online communication.
What is Network Scanning?
To troubleshoot audio delay in Zoom despite good internet speed, locate the source of data packet loss or latency.
In metaphorical terms, network scanning is similar to auditing done by a CA.
Network Scanning helps you do that. It lays out all the devices on the network, their performance and the traffic between them.
Network scanning is accomplished using a tool ( often called a network scanner) and a specialized individual with such skills.
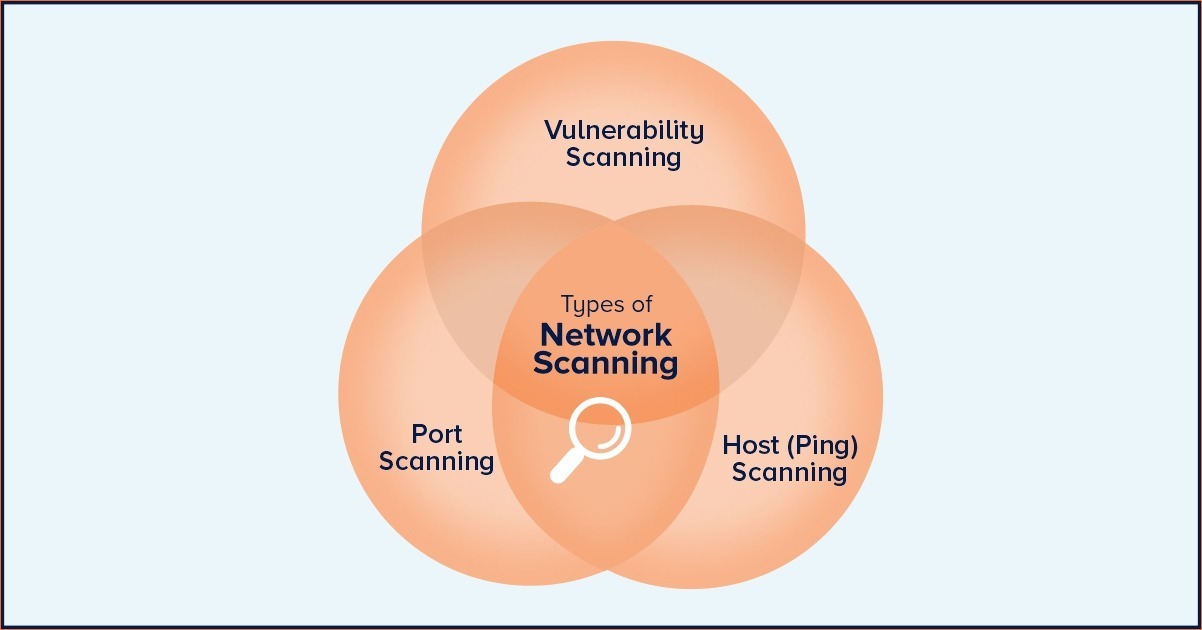
What are the types of Network Scanner?
Let’s explore the top three types of network scanners.
Ping Scanning.
Ping scanning is a network scanning technique used to determine devices’ online/offline status within a network or a range of IP addresses. It involves sending Internet Control Message Protocol (ICMP) Echo Request (ping) packets to target IP addresses and observing the responses.
Here’s how ping scanning works:
- Sending Ping Requests: The scanning tool or software sends ICMP Echo Request packets to various IP addresses or individual devices. These packets are typically referred to as “pings.”
- Receiving Responses: Online and reachable Devices will respond to ping requests with ICMP Echo Reply packets. These responses confirm the presence of an active device at the target IP address.
- No Responses: Devices that are offline, firewalled, or configured not to respond to ICMP Echo Requests will not generate a response. In this case, the scanning tool might interpret the lack of response as indicating that the target IP address is not in use or unreachable.
- Analysis: The results of the ping scan are analyzed to determine which IP addresses are currently active and responsive on the network.
Ping scanning is often used as a preliminary step in network reconnaissance to identify live hosts or devices before more detailed scanning techniques, such as port scanning, are applied. It’s a non-intrusive method that helps network administrators or security professionals understand the basic layout of a network and identify potential targets for further investigation.
Vulnerability Scanning.
Vulnerability scanning is a proactive practice involving specialized tools to find and assess computer systems, networks, and software weaknesses. These weaknesses, called vulnerabilities, could be exploited by hackers. The process includes:
- Identifying all assets in a network.
- Scanning for known vulnerabilities.
- Assessing the seriousness of these vulnerabilities.
- Generating reports for IT teams.
- Fixing or mitigating the vulnerabilities.
It’s an ongoing process to keep systems secure from evolving threats and is often required for compliance with industry regulations.
Port Scanning.
A port is like a virtual doorway where all network connections start and end. Think of it as a software-based address for network services. Each service, like a website or email, has its port managed by your computer’s operating system. Here are some important port numbers and what they’re used for.
Port Service
7 Echo Protocal
23 Telnet
25 SMTP (Emails)
Let’s talk about port scanning, like checking if these doors are open or closed.
NMAP is the most popular and useful port scanner. Port scanning sends special messages to specific ports to see if they respond.
It’s like knocking on doors to see if anyone’s home. It’s essential to understand what’s happening to protect your network.
Technically speaking, a port scanner sends a TCP or UDP network packet to a specific port to enquire about its status.
An expert can analyze these port scan results.
Need help with Network Scanning.
Decoding IT requires clients to undergo a network assessment, including a scan. This helps analyze requirements and identify growth opportunities.
As a Managed IT Service provider, we have been providing these services for decades and follow a rigorous onboarding process for clients.